#PHISHING
Cyber Security
IncidentRespond
malware
RAZWAN MOKHTAR
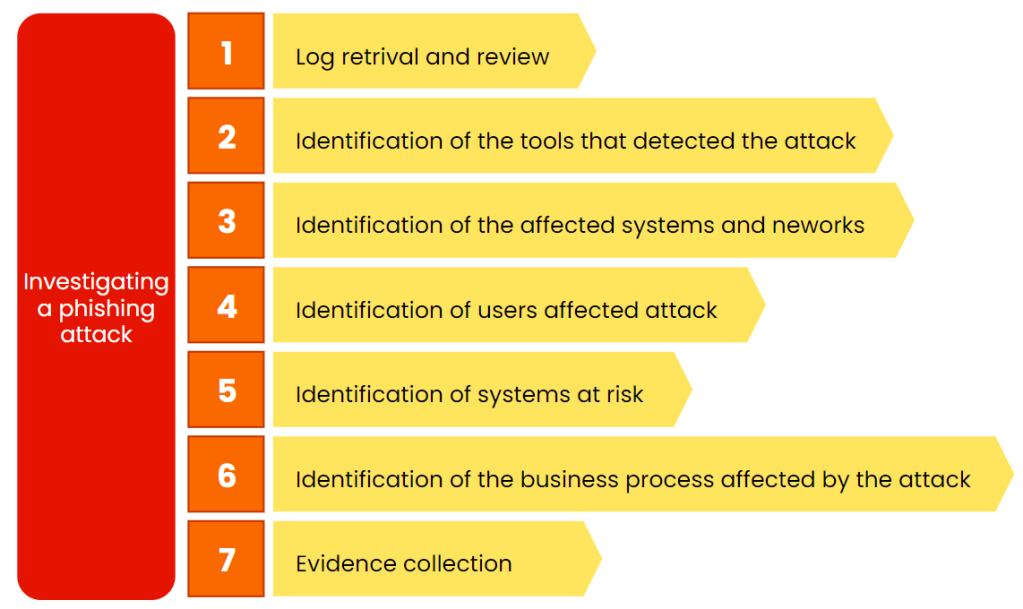
The investigation phase takes the following steps.
Phishing attack is expensive to handle, today I am sharing my investigation phase for phishing as presented in my recent workshop. I hope it will benefit for IR team.
- Log retrieval and review
- IR team received logs from security tools or the blue team from in the SOC operation team
- System logs help in providing important information such as IP addresses and ports from the source and destination assets
- It is important to identify the assets and the owner.
- Identification of the tools that detect the attack
- Get familiar with your environment and available tools to help in the investigation
- OODA Loop should be playing a bigger role here - from the Observation and Orient
- Tools should facilitated the detection of the attack
- Identification of the affected systems and networks
- Phishing involved social engineer whereby this is hard to detect because not everyone will work together in reporting such attack if they got infected by this type of attack
- Its hard to identify the compromised assets and its can quickly escalate
- To identify the affected systems and network are very crucial
- Move faster and efficient should be the right key in here
- Identification of users affected attack
- Please refer the organisation cybersecurity policy related to respond time in identifying the affected user
- Should identify what type of malware been using during this phishing attacks
- Create an investigation canvas if requires
- This activity and information should be shared with the communication team in IR
- Identification of systems at risk
- After identifying what type of attack and severity of the attack, IR team should know identify other systems that at risk
- Does the attacker managed to perform lateral movement?
- Do they have the same login and password for other machine?
- IR team should send notification telling to the affected users to changes new password
- Identification of the business processes affected by the attack
- After identifying the systems risk, IR team should use the information to identify which part of the incident affected the business process
- Example: the phishing attack managed to have access in web server for the employees to submit documents, therefore the IR team should identify business process that affected.
- Evidence collection
- IR teams needs to collect all such evidence to help with the analysis of the attack
- Prepare long term and short term recommendation if available.
